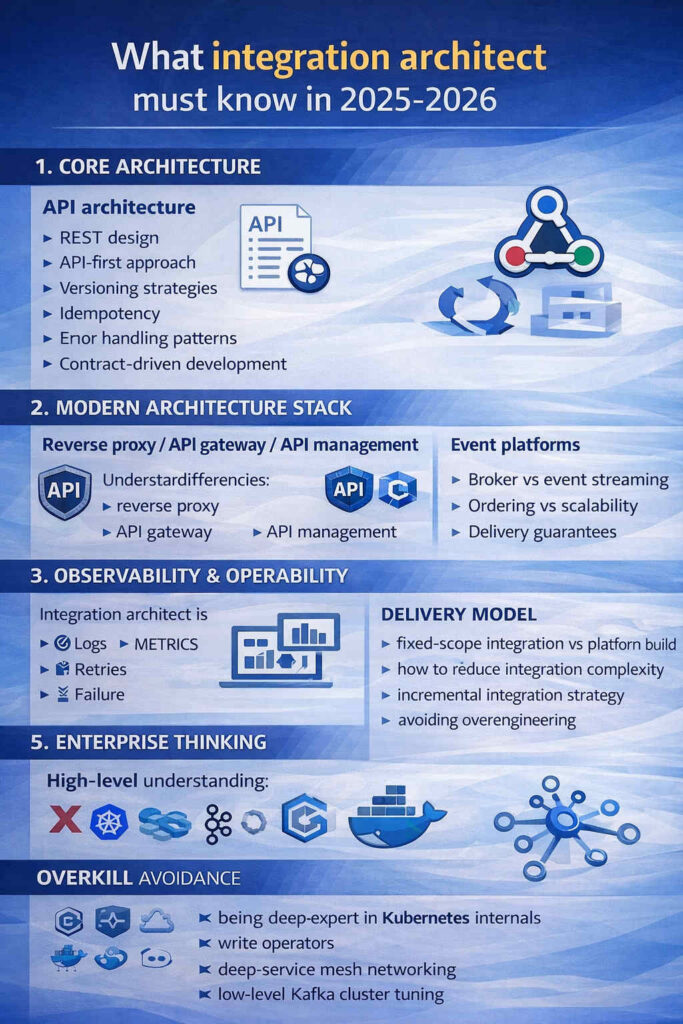
1. CORE ARCHITECTURE
API architecture
- REST design
- API-first approach
- versioning strategies
- idempotency
- error handling patterns
- contract-driven development
…more
API architecture remains one of the core foundations of modern system integration. In 2025–2026, APIs are no longer simply technical interfaces — they define how systems evolve, how teams collaborate, and how organizations expose capabilities internally and externally. A well-designed API becomes a stable boundary between systems, allowing change without creating unnecessary coupling. For integration architects, API design is less about syntax and more about creating clear contracts that support long-term maintainability.
REST design
REST design continues to be the dominant paradigm for many business integrations because of its simplicity and broad adoption. However, mature REST design goes beyond basic CRUD endpoints. Integration architects must think in terms of resource modeling, clear naming conventions, stateless interactions, predictable response structures, and proper use of HTTP semantics. Good REST design reduces ambiguity and makes APIs intuitive for both developers and automated systems. Consistency across APIs is often more valuable than theoretical purity.
API-first approach
An API-first approach means designing interfaces before implementing underlying services or integrations. This encourages clarity of requirements, improves collaboration between teams, and allows parallel development. In modern integration environments, API-first practices help organizations avoid tightly coupled solutions by establishing clear interaction models early. Documentation, contract definition, and interface review become part of the design process rather than an afterthought.
Versioning strategies
Change is inevitable, and versioning strategies are essential for managing evolution without breaking existing consumers. Integration architects must decide when to introduce new versions, how to communicate deprecation, and how long to support older interfaces. Versioning is not just a technical detail — it is a governance decision that affects operational stability and user trust. Pragmatic approaches often include backward-compatible changes where possible and clear lifecycle management for APIs.
Idempotency
Idempotency is a critical concept for reliable integrations, especially in distributed environments where retries and network failures are common. Designing endpoints so that repeated requests produce consistent results helps prevent data corruption and unexpected side effects. Integration architects should consider idempotency in operations like payments, order processing, and state transitions, where accidental duplication can have serious consequences. Proper use of identifiers, tokens, or request keys helps maintain safe retry behavior.
Error handling patterns
Clear and consistent error handling is essential for operability. APIs should communicate failures in predictable ways, using structured error responses that allow clients to understand what went wrong and how to react. This includes meaningful status codes, machine-readable error messages, and clear separation between validation errors, business rule violations, and system failures. Good error design improves debugging, monitoring, and overall reliability of integration workflows.
Contract-driven development
Contract-driven development focuses on defining and maintaining explicit API contracts that both providers and consumers rely on. Tools such as OpenAPI specifications help ensure shared understanding between teams and reduce ambiguity during implementation. By treating the contract as a primary artifact, integration architects can enable testing, automation, and governance around interface changes. This approach strengthens collaboration and helps prevent breaking changes from propagating across complex integration landscapes.
Sync vs Async integration
You must know when to use:
- REST sync
- async messaging
- event-driven
- latency vs consistency trade-offs
…more
Understanding when to use synchronous or asynchronous integration patterns is one of the most important skills for an integration architect. Modern system landscapes often combine multiple communication models, and choosing the wrong one can lead to unnecessary complexity, performance bottlenecks, or fragile dependencies between systems. Rather than following trends, architects must evaluate business requirements, operational constraints, and system characteristics to determine the appropriate approach.
REST synchronous integration
Synchronous integrations, typically implemented through REST APIs, are well suited for scenarios where immediate responses are required and workflows depend on direct feedback. Examples include user-facing operations, validation checks, or transactional processes where a client needs a result before continuing. The advantages of synchronous communication include simplicity, clear request-response semantics, and easier reasoning about flow execution. However, synchronous systems create tighter coupling and can introduce cascading failures if downstream services become slow or unavailable.
Asynchronous messaging
Asynchronous messaging introduces decoupling between systems by allowing producers and consumers to communicate through message brokers or queues. This pattern is useful when workloads must be processed independently of immediate user interaction or when reliability and resilience are more important than instant responses. Messaging allows systems to handle spikes in load, recover from temporary failures through retries, and evolve independently. Integration architects must consider delivery guarantees, retry strategies, and message design to ensure predictable behavior.
Event-driven integration
Event-driven architectures extend asynchronous messaging by focusing on the publication of events that represent state changes within a system. Instead of directly requesting actions, systems react to events emitted by others. This approach improves scalability and flexibility, especially in distributed environments, but also introduces complexity around event ordering, data consistency, and monitoring. Architects must ensure that event-driven designs are introduced for real decoupling needs rather than as a default architectural choice.
Latency vs consistency trade-offs
One of the central decisions in integration architecture is balancing latency and consistency. Synchronous integrations typically provide immediate consistency but may suffer from higher latency and tighter dependencies. Asynchronous and event-driven models often improve responsiveness and resilience but introduce eventual consistency, requiring careful design of data synchronization and error recovery mechanisms. Understanding these trade-offs allows architects to align integration patterns with business priorities, such as user experience, reliability, or scalability.
Combining patterns pragmatically
In practice, most integration landscapes use a hybrid approach combining synchronous APIs with asynchronous messaging and event-driven workflows. Integration architects should avoid rigid adherence to a single paradigm and instead focus on selecting the simplest model that satisfies requirements. A pragmatic architecture often begins with synchronous integration for clarity and introduces asynchronous mechanisms where operational needs — such as resilience, scalability, or decoupling — justify the additional complexity.
Integration patterns
- API facade
- anti-corruption layer
- orchestration vs choreography
- canonical model vs mapping
- pub/sub vs queue
…more
Integration patterns provide a shared architectural language that helps integration architects design systems in a structured and predictable way. Rather than inventing new solutions for every project, experienced architects rely on proven patterns to address recurring challenges such as coupling, system evolution, data transformation, and communication coordination. Understanding when and why to apply these patterns is often more important than mastering any specific technology.
API facade
The API facade pattern introduces a simplified interface that sits in front of one or multiple underlying services or systems. Its primary purpose is to hide internal complexity and present a stable, consumer-friendly contract. This is especially useful when integrating legacy systems or multiple backend services that expose inconsistent interfaces. An API facade can aggregate responses, normalize data structures, enforce security policies, or provide version stability while internal systems evolve. For integration architects, this pattern helps decouple external consumers from internal implementation details.
Anti-corruption layer
An anti-corruption layer (ACL) protects one domain model from being tightly coupled to another, especially when integrating modern systems with legacy platforms. Instead of allowing external data structures or business logic to leak into internal systems, the ACL translates between models and enforces boundaries. This reduces the risk of long-term architectural degradation and helps maintain clean domain separation. Integration architects often apply this pattern when introducing new systems into existing environments, allowing gradual migration without forcing immediate changes across the entire landscape.
Orchestration vs choreography
Orchestration and choreography represent two different ways of coordinating interactions between services. Orchestration relies on a central component that controls the workflow and manages execution steps, making it easier to understand and monitor complex processes. Choreography, on the other hand, distributes coordination across multiple services that react to events independently. While choreography can improve scalability and decoupling, it may also increase complexity and reduce visibility into overall process flow. Integration architects must evaluate the domain complexity, operational requirements, and team maturity when choosing between these approaches.
Canonical model vs mapping
When multiple systems exchange data, architects must decide whether to introduce a canonical data model or rely on direct mappings between systems. A canonical model establishes a shared representation of core business entities, which can simplify integration in large environments but requires governance and discipline. Direct mapping strategies may be simpler for smaller integrations but can become difficult to maintain as the number of connections grows. The right choice depends on scale, organizational structure, and expected system evolution.
Pub/Sub vs queue
Messaging patterns also require architectural decisions between publish/subscribe (pub/sub) and queue-based communication. Queue patterns are typically used for task processing where a message is handled by a single consumer, ensuring controlled execution and workload distribution. Pub/sub patterns broadcast events to multiple subscribers, enabling reactive and loosely coupled system behavior. Integration architects must consider factors such as ordering, scalability, delivery guarantees, and consumer independence when selecting between these models. Often, both patterns coexist within the same integration architecture, each serving different purposes.
Identity basics
- OAuth2 flows
- OpenID Connect
- service-to-service auth
- API security patterns
…more
Identity and access management have become essential components of modern integration architecture. As systems grow more distributed and APIs are exposed across organizational boundaries, security can no longer be treated as an afterthought. Integration architects must understand identity fundamentals well enough to design secure communication patterns, enforce trust boundaries, and prevent unauthorized access without introducing unnecessary complexity.
OAuth2 flows
OAuth2 has become the standard framework for delegated authorization in API-driven environments. Rather than sharing credentials directly between systems, OAuth2 allows controlled access through tokens issued by an authorization server. Integration architects do not need to implement OAuth2 internals, but they must understand the common flows — such as authorization code, client credentials, and device flows — and know when each is appropriate. Choosing the correct flow affects user experience, security posture, and operational complexity.
OpenID Connect
OpenID Connect builds on OAuth2 by adding authentication capabilities, allowing systems to verify user identity in a standardized way. In integration scenarios, OpenID Connect often enables single sign-on (SSO), centralized identity providers, and secure user context propagation across services. Architects should understand concepts such as ID tokens, identity claims, and federation between identity providers, ensuring that authentication responsibilities remain centralized rather than duplicated across multiple systems.
Service-to-service authentication
As architectures evolve toward distributed systems and microservices, service-to-service authentication becomes increasingly important. Machine-to-machine communication typically relies on token-based authentication using client credentials or mutual TLS. Integration architects must ensure that services authenticate each other securely while maintaining automation-friendly workflows. Proper token lifecycle management, secure storage of secrets, and clearly defined trust relationships are critical to avoiding vulnerabilities.
API security patterns
Beyond identity protocols, API security involves a broader set of architectural considerations. These include enforcing least-privilege access, validating input data, protecting against abuse through rate limiting, and using API gateways or proxies to centralize policy enforcement. Architects should also consider zero-trust principles, where every request is verified regardless of network location. The goal is not to create overly complex security mechanisms but to establish consistent, maintainable patterns that reduce risk while supporting scalability.
Security as part of architecture
Modern integration architecture treats identity and security as integral design elements rather than implementation details. Early decisions about authentication methods, token propagation, and access control models influence system maintainability and future extensibility. By incorporating identity considerations from the beginning, integration architects can reduce friction between teams, simplify compliance requirements, and ensure that integrations remain secure as systems evolve.
2. MODERN ARCHITECTURE STACK
Reverse proxy / API gateway / API management
Understand differencies:
- reverse proxy — traffic routing
- API gateway — policy enforcement + aggregation
- API management — governance
…more
Modern integration architectures frequently rely on intermediary layers that sit between clients and backend services. Reverse proxies, API gateways, and API management platforms are often mentioned together, but they serve different architectural purposes. A senior integration architect must understand not only what each component does, but also when introducing them adds real value — and when it simply increases complexity without clear benefit.
Reverse proxy — traffic routing and edge control
A reverse proxy primarily acts as an entry point that forwards incoming requests to backend services. Its responsibilities typically include traffic routing, load balancing, TLS termination, caching, and basic security controls. Reverse proxies help simplify infrastructure by hiding internal service structures and presenting a unified external endpoint. For many small or medium integrations, a well-configured reverse proxy can provide sufficient functionality without introducing heavier architectural layers. Understanding this simplicity is important, because not every integration requires a full API gateway solution.
API gateway — policy enforcement and aggregation
An API gateway builds on reverse proxy capabilities by adding application-level functionality. Beyond routing traffic, API gateways enforce authentication and authorization policies, apply rate limiting, manage request transformations, and aggregate responses from multiple services. They can also centralize cross-cutting concerns such as logging, monitoring, and request validation. Integration architects use API gateways when there is a need for consistent policy enforcement across multiple APIs or when external consumers require a unified interface that hides internal service complexity.
API management — governance and lifecycle control
API management platforms operate at a broader organizational level. While they may include gateway functionality, their main focus is governance: managing API lifecycle, documentation, versioning, access control, analytics, and developer onboarding. API management introduces structure around how APIs are published, consumed, and evolved over time. This becomes particularly important in enterprise environments or multi-team organizations where APIs are treated as products and require formal governance models.
Choosing the right layer
A key architectural skill is recognizing that these layers are not interchangeable. Reverse proxies address infrastructure-level needs, API gateways address runtime policy and integration concerns, and API management addresses organizational governance. Introducing all three without clear requirements can lead to unnecessary operational overhead. Integration architects must evaluate scale, security requirements, team structure, and long-term API strategy before selecting the appropriate approach.
Pragmatic adoption
In many real-world projects, architectures evolve incrementally. A system may begin with a reverse proxy for simplicity, introduce gateway features as APIs grow, and adopt API management later when governance needs arise. This pragmatic progression allows organizations to balance flexibility with operational maturity. The goal is not to deploy the most advanced tooling but to introduce the right level of control at the right time, ensuring that integrations remain manageable and aligned with business goals.
Event platforms
You should understand:
- broker vs event streaming
- ordering vs scalability
- delivery guarantees
- when RabbitMQ simpler than Kafka
…more
Event platforms play an increasingly important role in modern integration architecture, especially as organizations move toward distributed systems and asynchronous communication. However, adopting event-driven approaches requires careful architectural thinking rather than simply choosing a popular technology. Integration architects must understand the conceptual differences between messaging models, evaluate trade-offs, and select the simplest solution that meets the operational and business requirements.
Broker vs event streaming
Traditional message brokers and event streaming platforms solve different problems, even though they are often discussed together. Message brokers, such as RabbitMQ, focus on reliable delivery of tasks or messages between producers and consumers. They are typically well suited for workflow orchestration, background processing, and decoupling services through queues. Event streaming platforms, such as Kafka, emphasize durable event logs and high-throughput streaming, allowing multiple consumers to process historical and real-time data independently. Integration architects must recognize whether the use case is task-oriented communication or continuous event processing before selecting an approach.
Ordering vs scalability
One of the key trade-offs in event platforms is balancing message ordering with scalability. Strict ordering guarantees can simplify processing logic but may limit throughput and parallelization. Highly scalable systems often distribute events across partitions, which improves performance but introduces complexity in maintaining order. Architects need to evaluate whether business processes truly require global ordering or whether localized ordering within partitions is sufficient. Understanding this trade-off helps avoid overengineering solutions that introduce unnecessary constraints.
Delivery guarantees
Event platforms provide different delivery semantics, such as at-most-once, at-least-once, or exactly-once processing. Each comes with operational implications and complexity trade-offs. For example, at-least-once delivery is common and generally easier to implement but requires idempotent consumers to avoid duplicate processing. Exactly-once semantics can reduce duplication risks but may introduce additional complexity and performance overhead. Integration architects must align delivery guarantees with real business needs rather than defaulting to the most complex option.
When RabbitMQ is simpler than Kafka
A common architectural mistake is adopting highly scalable event streaming platforms when a simpler message broker would be more appropriate. RabbitMQ and similar brokers are often easier to operate, require less infrastructure expertise, and provide sufficient capabilities for many integration scenarios such as asynchronous workflows, background processing, or service decoupling. Kafka becomes valuable when handling high-throughput data streams, long-lived event histories, or complex data pipelines. Senior integration architects recognize that choosing the simplest viable solution often leads to better maintainability and lower operational risk.
Pragmatic event-driven design
Event-driven architecture should be introduced intentionally and incrementally. Not every integration benefits from event streaming, and overusing event patterns can make systems harder to understand and operate. A pragmatic approach starts with clear use cases — such as decoupling, scalability, or resilience — and evaluates whether asynchronous messaging or event streaming genuinely improves the architecture. By focusing on outcomes rather than tools, integration architects can design systems that are both robust and maintainable.
Microservices reality
- bounded contexts
- data ownership
- distributed failure modes
- why not everything should be microservices
…more
Microservices have become a widely adopted architectural approach, but real-world experience has shown that they introduce both opportunities and significant challenges. For integration architects, understanding the practical realities of microservices is more important than following trends. Successful architectures focus on clear system boundaries, operational simplicity, and organizational alignment rather than blindly decomposing systems into smaller services.
Bounded contexts
One of the most important principles behind microservices is the concept of bounded contexts. Services should be defined around clear business domains rather than technical layers or arbitrary functional splits. A bounded context establishes ownership over specific business capabilities and allows teams to evolve services independently without creating tight coupling. Integration architects must ensure that service boundaries reflect domain logic and organizational structure, as poorly defined boundaries often lead to excessive inter-service communication and increased complexity.
Data ownership
In a microservices architecture, each service typically owns its data and controls access to it through defined APIs or events. This principle helps avoid shared databases and hidden dependencies, enabling services to evolve independently. However, strict data ownership introduces new challenges such as data duplication, synchronization strategies, and eventual consistency. Integration architects must carefully design how data flows between services, ensuring that responsibilities remain clear while minimizing unnecessary data coupling.
Distributed failure modes
Unlike monolithic systems, microservices operate in distributed environments where network failures, latency issues, and partial outages are normal conditions rather than exceptions. Integration architects must anticipate these failure modes and design resilience into the system. This includes implementing timeouts, retries, circuit breakers, and fallback strategies, as well as ensuring that monitoring and observability provide visibility into cross-service interactions. Understanding distributed failure patterns is essential for preventing cascading failures that can impact entire platforms.
Why not everything should be microservices
Despite their popularity, microservices are not a universal solution. They introduce operational overhead, increase system complexity, and require mature deployment, monitoring, and organizational practices. For smaller systems or straightforward business domains, simpler architectures — such as modular monoliths or well-structured APIs — may provide better long-term maintainability. Senior integration architects understand that the goal is not to adopt microservices by default but to choose the architectural style that best fits the scale, team structure, and business needs.
Pragmatic architectural thinking
The most effective integration strategies treat microservices as one tool among many rather than as an architectural ideology. A pragmatic approach evaluates whether service decomposition genuinely improves scalability, team autonomy, or system evolution. Often, systems evolve gradually, starting with simpler architectures and introducing microservices where clear boundaries and operational maturity exist. This incremental mindset helps organizations avoid unnecessary complexity while still benefiting from distributed architectures when they provide real value.
Cloud integration patterns
- serverless integration
- managed messaging
- identity integration
- cloud storage events
…more
Cloud platforms have fundamentally changed how integrations are designed and operated. Instead of building and maintaining infrastructure-heavy integration layers, organizations increasingly rely on managed services that reduce operational overhead while improving scalability and resilience. For integration architects, the focus is not simply on using cloud technologies, but on understanding patterns that allow systems to evolve flexibly while maintaining clarity and control.
Serverless integration
Serverless architectures enable event-driven or API-based integrations without requiring dedicated infrastructure management. Functions triggered by HTTP requests, events, or scheduled processes allow teams to implement lightweight integration logic that scales automatically based on demand. Serverless integration can be especially useful for data transformation, workflow automation, or connecting external APIs. However, integration architects must also consider aspects such as execution limits, cold-start latency, and observability challenges to ensure that serverless solutions remain reliable in production environments.
Managed messaging
Cloud providers offer managed messaging services that simplify asynchronous communication between systems. These services provide built-in scalability, delivery guarantees, and operational monitoring without requiring teams to operate their own messaging infrastructure. Managed queues, topics, and event buses allow integration architects to decouple services while reducing maintenance complexity. The architectural challenge is deciding when managed messaging provides sufficient flexibility and when more specialized event platforms are necessary for advanced use cases.
Identity integration
Identity integration is a key component of cloud-based architectures. Cloud identity services allow centralized authentication, authorization, and user management across multiple applications and APIs. Integration architects must understand how identity providers interact with APIs through tokens, roles, and access policies, enabling secure service-to-service communication and user authentication flows. Proper identity integration reduces duplication of security logic across systems and helps organizations implement consistent access control models.
Cloud storage events
Modern cloud storage platforms often support event-driven triggers when files are created, modified, or deleted. These storage events can initiate workflows such as data processing pipelines, document validation, or automated synchronization between systems. By leveraging storage events, integration architects can design reactive architectures that eliminate manual polling and improve efficiency. However, careful design is required to handle retries, duplicate events, and consistency considerations when building workflows around storage triggers.
Designing cloud-native integrations
Cloud integration patterns emphasize composability — combining small, managed services into flexible workflows rather than building monolithic integration layers. Architects must balance the advantages of managed services with concerns about portability, vendor-specific features, and long-term maintainability. A pragmatic cloud-native approach focuses on using platform capabilities where they provide clear benefits while maintaining architectural clarity and avoiding unnecessary complexity.
3. OBSERVABILITY & OPERABILITY
Integration architect is thinking about operations:
- structured logging
- metrics vs logs vs traces
- failure visibility
- retry strategies
- dead-letter queues
…more
A key shift in modern integration architecture is the recognition that building integrations is only part of the work — operating them reliably over time is equally important. Integration architects must design systems with operational realities in mind from the beginning. Observability and operability are not optional enhancements but core architectural concerns that determine how easily issues can be detected, diagnosed, and resolved in distributed environments.
Structured logging
Structured logging provides machine-readable logs that allow systems to be monitored and analyzed efficiently. Instead of unstructured text messages, structured logs include consistent fields such as timestamps, request identifiers, correlation IDs, and contextual metadata. This enables better filtering, searching, and aggregation across multiple services. Integration architects should encourage consistent logging standards across systems to simplify debugging and improve operational visibility, especially when workflows span multiple components.
Metrics vs logs vs traces
Understanding the differences between metrics, logs, and traces is essential for effective observability. Metrics provide high-level insights into system health and performance trends, such as latency or error rates. Logs capture detailed events and contextual information that help explain what happened during execution. Distributed traces connect multiple service calls into a single flow, showing how requests move through the system. Integration architects must ensure that these signals complement each other, providing both overview monitoring and deep diagnostic capabilities.
Failure visibility
In distributed integration environments, failures are inevitable. The goal is not to eliminate failures entirely but to make them visible and understandable. Clear error reporting, alerting mechanisms, and monitoring dashboards help teams identify issues before they escalate into larger incidents. Integration architects should design systems that expose meaningful operational signals rather than hiding errors behind silent retries or unclear responses. Visibility into failures enables faster response times and improves system resilience.
Retry strategies
Retries are a common mechanism for handling transient failures such as network issues or temporary service outages. However, poorly designed retry logic can create cascading problems, including duplicated operations or system overload. Architects must define retry policies carefully, considering exponential backoff, maximum retry limits, and idempotency requirements. Integrations should distinguish between temporary errors that can be retried safely and permanent failures that require alternative handling.
Dead-letter queues
Dead-letter queues (DLQs) provide a controlled mechanism for handling messages that cannot be processed successfully after retries. Instead of losing data or endlessly retrying failed messages, DLQs isolate problematic cases for later analysis and manual intervention. This approach improves system reliability and prevents operational bottlenecks. Integration architects should design workflows that include clear processes for monitoring and resolving dead-letter messages, ensuring that operational teams can respond effectively.
Operational mindset
Ultimately, observability and operability reflect a broader architectural mindset: integrations are living systems that must be monitored, maintained, and evolved over time. By incorporating operational considerations into design decisions — from logging standards to error handling strategies — integration architects enable organizations to operate integrations confidently and sustainably in complex environments.
4. DELIVERY MODEL
- fixed-scope integration vs platform build
- how to reduce integration complexity
- incremental integration strategy
- avoiding overengineering
…more
Integration architecture is not only about technical design — it also involves choosing the right delivery approach. The way integrations are planned, scoped, and implemented directly influences cost, timelines, maintainability, and long-term success. A senior integration architect must understand how to balance business expectations with technical reality, selecting delivery models that provide value without creating unnecessary complexity or long-term risk.
Fixed-scope integration vs platform build
One of the most important decisions is distinguishing between focused integrations and building a broader integration platform. Fixed-scope integrations typically involve connecting a limited number of systems to solve a clearly defined business problem. These projects benefit from well-defined scope, predictable timelines, and pragmatic architecture. In contrast, platform-building initiatives aim to create reusable infrastructure or standardized integration layers across an organization. While platforms can offer long-term benefits, they require higher investment, governance, and organizational maturity. Integration architects must carefully evaluate whether a problem truly requires a platform or whether a simpler targeted solution is more appropriate.
Reducing integration complexity
Complexity often emerges unintentionally when systems are connected without clear architectural boundaries. A key responsibility of the integration architect is to actively reduce complexity rather than adding layers of abstraction by default. This includes minimizing unnecessary intermediaries, avoiding excessive transformations, and selecting integration patterns that remain understandable over time. Simplicity improves maintainability, accelerates onboarding for new team members, and reduces operational risk.
Incremental integration strategy
Large integration initiatives are rarely successful when delivered as monolithic projects. Instead, incremental strategies allow organizations to deliver value step by step, validating assumptions and adjusting architecture as requirements evolve. Integration architects should encourage iterative delivery, starting with minimal viable integrations and gradually expanding capabilities. This approach reduces risk, enables faster feedback cycles, and prevents organizations from overcommitting to architectural decisions before they are fully validated.
Avoiding overengineering
A common challenge in integration projects is the temptation to introduce advanced technologies or complex patterns prematurely. Overengineering can result from adopting trends without clear justification or attempting to anticipate every possible future requirement. Senior integration architects prioritize pragmatic solutions that solve current problems while remaining adaptable to change. Introducing complexity only when it delivers measurable value helps maintain clarity and ensures that systems remain manageable for both development and operations teams.
Aligning architecture with business outcomes
Ultimately, the delivery model should align technical decisions with business objectives. Integration architects must consider factors such as team capabilities, operational maturity, budget constraints, and long-term ownership. By choosing delivery strategies that emphasize clarity, incremental progress, and practical outcomes, architects help organizations achieve reliable integrations without unnecessary overhead or prolonged project timelines.
5. ENTERPRISE THINKING
High-level understanding:
- API governance
- version lifecycle
- domain boundaries
- data contracts
…more
Enterprise integration architecture requires a broader perspective than individual system connections or isolated projects. As organizations grow, integrations must support multiple teams, evolving business processes, and long-term system evolution. Enterprise thinking involves understanding how architectural decisions scale across domains, how standards are maintained over time, and how systems remain manageable even as complexity increases. Integration architects operating at this level focus on creating clarity, consistency, and governance without introducing unnecessary bureaucracy.
API governance
API governance establishes guidelines and practices that ensure consistency and quality across an organization’s APIs. This includes naming conventions, security policies, documentation standards, lifecycle management, and review processes. Effective governance does not mean rigid control but rather providing guardrails that help teams build interoperable and maintainable interfaces. Integration architects must balance flexibility and standardization, enabling teams to innovate while preventing fragmentation or incompatible implementations that complicate long-term integration.
Version lifecycle
Managing API evolution is a critical enterprise concern. Over time, APIs change as business requirements evolve, new capabilities are introduced, or technical improvements are implemented. A clear version lifecycle defines how APIs are introduced, updated, deprecated, and eventually retired. Integration architects must design strategies that allow change without breaking existing consumers, such as backward compatibility, phased deprecation, and clear communication with stakeholders. Well-managed version lifecycles reduce operational disruption and build trust with internal and external API consumers.
Domain boundaries
Enterprise architectures often involve multiple domains representing different business capabilities. Defining clear domain boundaries helps reduce coupling between teams and systems by establishing ownership and responsibility for specific areas. Integration architects use domain-driven thinking to prevent uncontrolled data sharing or tightly intertwined workflows. Clear boundaries enable independent evolution of systems while maintaining consistent integration through well-defined interfaces.
Data contracts
Data contracts define the structure, semantics, and expectations of information exchanged between systems. In enterprise environments, shared understanding of data is essential to avoid misinterpretation and integration errors. Contracts help ensure that producers and consumers align on formats, validation rules, and lifecycle expectations. Integration architects promote the use of explicit data contracts to support automation, testing, and governance, enabling organizations to evolve systems without introducing hidden dependencies.
Long-term architectural perspective
Enterprise thinking ultimately emphasizes sustainability. Integration architects must consider how decisions made today will impact future system evolution, organizational scaling, and operational stability. Rather than optimizing for short-term solutions alone, enterprise architecture aims to create structures that remain adaptable over time. By applying governance thoughtfully, respecting domain boundaries, and managing API and data lifecycles carefully, integration architects help organizations maintain control over complex integration landscapes.
OVERKILL — where you should not deep dive
Not so important to know as subject matter expert in details:
- being deep expert in Kubernetes internals
- write operators
- deep service mesh networking
- low-level Kafka cluster tuning
- multi-cloud expert
This is a platform engineer territory.
…more
One of the most important skills for a senior integration architect is knowing not only what to learn, but also what not to specialize in too deeply. Modern technology landscapes are vast, and attempting to become a deep expert in every infrastructure or platform detail is neither realistic nor necessary. Integration architecture focuses primarily on designing interactions between systems, defining boundaries, and making pragmatic decisions that reduce complexity. Understanding where to draw the line between architectural knowledge and platform engineering expertise is essential for maintaining focus and effectiveness.
Not every technical area requires deep specialization
Integration architects benefit from broad technical awareness across infrastructure, cloud platforms, and distributed systems. However, deep expertise in low-level implementation details is often the responsibility of specialized roles such as platform engineers, DevOps engineers, or site reliability engineers. The architect’s role is to understand capabilities, limitations, and trade-offs at a conceptual level rather than managing operational internals or optimizing infrastructure configurations.
Kubernetes internals and operator development
Kubernetes has become a common deployment platform, and integration architects should understand its high-level concepts — such as containers, scaling, service discovery, and deployment patterns. However, deep knowledge of Kubernetes internals, custom resource definitions, or writing operators is typically unnecessary unless the role directly involves platform engineering. Architects should focus on how integrations behave within containerized environments rather than mastering cluster-level mechanics.
Deep service mesh networking
Service meshes introduce advanced capabilities such as traffic management, resilience policies, and observability across microservices. While architects should understand the purpose and implications of service mesh adoption, deep expertise in networking internals, sidecar configuration, or low-level performance tuning is generally beyond the scope of integration architecture. The primary concern is evaluating whether a service mesh solves real architectural problems, not becoming a specialist in its internal mechanics.
Low-level Kafka cluster tuning
Event streaming platforms like Kafka can require significant operational expertise, including cluster management, partition balancing, and performance optimization. Integration architects should understand event-driven design patterns and messaging trade-offs but do not need to specialize in infrastructure-level tuning. These responsibilities are better handled by platform teams responsible for maintaining reliable infrastructure.
Multi-cloud expertise as infrastructure specialization
While architects may design integrations that span multiple cloud providers, becoming a deep multi-cloud infrastructure expert is rarely necessary. Integration architects should focus on cloud integration patterns, identity integration, and service capabilities rather than mastering every provider’s low-level services or operational tooling. Broad understanding enables informed architectural decisions without diverting attention away from integration strategy.
Staying focused on architectural value
Avoiding over-specialization allows integration architects to concentrate on their primary value: making clear architectural decisions that simplify system interaction and support long-term evolution. By maintaining high-level awareness without diving too deeply into platform engineering domains, architects can collaborate effectively with specialized teams while preserving a holistic view of the integration landscape.
Mental model of integration architect
You are not a tool specialist, but a decision maker who reduces complexity.
…more
The core mindset of a modern integration architect is fundamentally different from that of a tool specialist or technology evangelist. While tools and platforms are important, they are not the primary focus. The real value of an integration architect lies in making informed decisions that reduce complexity, improve clarity, and enable systems to evolve sustainably over time. In 2025–2026, successful integration work is less about mastering specific products and more about understanding patterns, trade-offs, and organizational realities.
From tool selection to decision-making
Many technical roles emphasize expertise in particular frameworks or platforms. Integration architecture, however, requires a broader perspective. Tools change quickly, but architectural principles remain relatively stable. The architect’s responsibility is to evaluate whether a specific technology genuinely solves a problem or simply adds another layer of abstraction. This means asking questions about long-term maintainability, operational impact, team capabilities, and business outcomes rather than focusing solely on technical features.
Reducing complexity instead of adding it
Integration projects often become complicated because multiple systems, teams, and requirements intersect. Without careful design, integrations can accumulate unnecessary layers, inconsistent data models, and fragile dependencies. A key skill of an integration architect is recognizing when complexity is unavoidable and when it is self-inflicted. By simplifying interfaces, choosing clear patterns, and avoiding premature optimization, architects help organizations maintain systems that remain understandable and maintainable over time.
Thinking in trade-offs
Architectural decisions rarely have perfect solutions. Every choice introduces trade-offs between flexibility, performance, cost, scalability, and operational effort. The integration architect’s mental model focuses on understanding these trade-offs and selecting options that align with the organization’s priorities. For example, choosing synchronous APIs may simplify implementation but reduce resilience, while event-driven architectures increase flexibility but add operational complexity. The role involves balancing these considerations rather than pursuing idealized designs.
Aligning technology with business context
Integration architecture exists at the intersection of technology and business needs. Decisions about APIs, messaging, or system boundaries should reflect organizational structure, delivery speed, and operational maturity. A solution that works well in a large enterprise environment may be unnecessarily complex for a smaller team. By aligning architecture with context, integration architects ensure that systems remain practical and sustainable rather than overly ambitious or under-engineered.
Collaboration and shared understanding
Reducing complexity also involves improving communication between teams. Integration architects help establish shared language through patterns, contracts, and consistent design principles. This reduces misunderstandings and enables teams to work independently while maintaining interoperability. The architect’s role is not only technical but also facilitative, helping teams align around clear integration strategies.
Architecture as continuous evolution
Finally, the mental model of an integration architect recognizes that architecture is not a one-time decision but an ongoing process. Systems evolve, requirements change, and new technologies emerge. By focusing on simplicity, adaptability, and clear boundaries, integration architects create environments where change can occur without constant rework. The ultimate goal is not to build the most advanced system, but to create one that remains manageable and adaptable as the organization grows.